Maximizing Security: Why Colleges & Universities Should Hire a Managed Security Services Provider
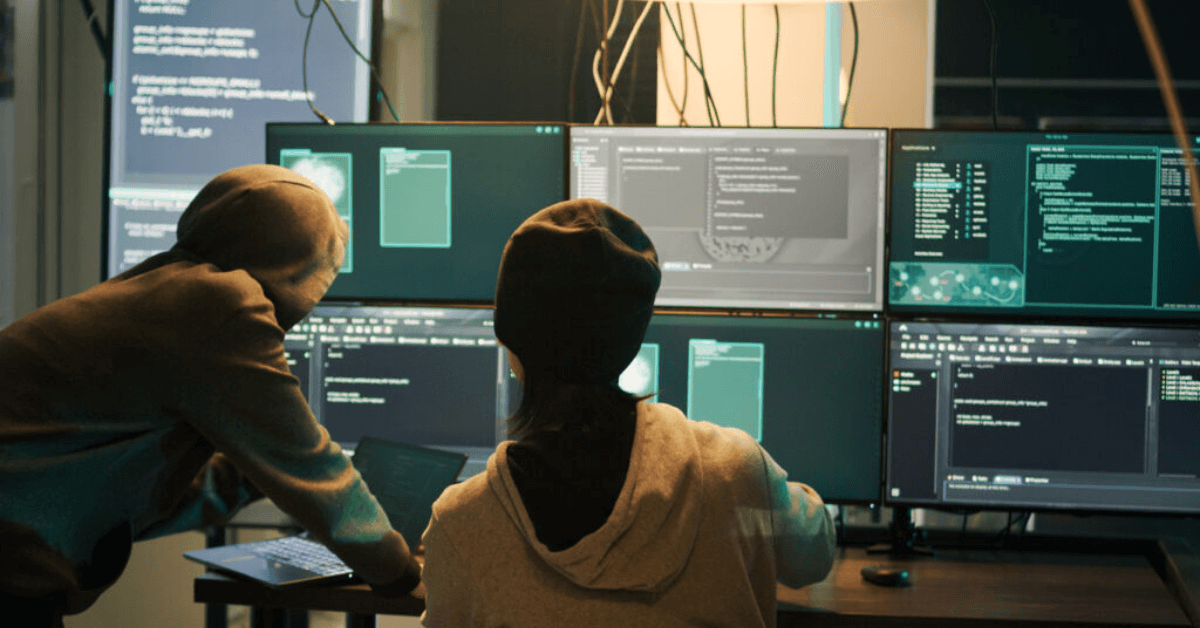
Maximizing Security: Why Colleges & Universities Should Hire a Managed Security Services Provider Colleges and universities play a vital role in fostering innovation, research, and education. However, they are increasingly becoming targets for cybercriminals due to their often weak security measures, valuable research data, and personal information. Hiring a managed security services provider (MSSP) can … Read more